Cyber Liability Insurance: An Essential and Urgently Needed Business Investment
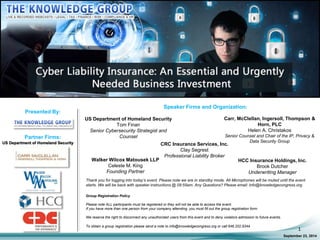
- 1. Speaker Firms and Organization: Carr, McClellan, Ingersoll, Thompson & Horn, PLC Helen A. Christakos Senior Counsel and Chair of the IP, Privacy & Data Security Group US Department of Homeland Security Tom Finan Senior Cybersecurity Strategist and Counsel Thank you for logging into today’s event. Please note we are in standby mode. All Microphones will be muted until the event starts. We will be back with speaker instructions @ 09:55am. Any Questions? Please email: Info@knowledgecongress.org Group Registration Policy Please note ALL participants must be registered or they will not be able to access the event. If you have more than one person from your company attending, you must fill out the group registration form. We reserve the right to disconnect any unauthorized users from this event and to deny violators admission to future events. To obtain a group registration please send a note to info@knowledgecongress.org or call 646.202.9344. Presented By: 1 September 23, 2014 Partner Firms: Walker Wilcox Matousek LLP Celeste M. King Founding Partner HCC Insurance Holdings, Inc. Brook Dutcher Underwriting Manager CRC Insurance Services, Inc. Clay Segrest Professional Liability Broker US Department of Homeland Security
- 2. If you experience any technical difficulties during today’s WebEx session, please contact our Technical Support @ 866-779-3239. 2 Follow us on Twitter, that’s @Know_Group to receive updates for this event as well as other news and pertinent info. You may ask a question at anytime throughout the presentation today via the chat window on the lower right hand side of your September 23, 2014 screen. Questions will be aggregated and addressed during the Q&A segment. Please note, this call is being recorded for playback purposes. If anyone was unable to log in to the online webcast and needs to download a copy of the PowerPoint presentation for today’s event, please send an email to: info@knowledgecongress.org. If you’re already logged in to the online webcast, we will post a link to download the files shortly. If you are listening on a laptop, you may need to use headphones as some laptops speakers are not sufficiently amplified enough to hear the presentations. If you do not have headphones and cannot hear the webcast send an email to info@knowledgecongress.org and we will send you the dial in phone number.
- 3. About an hour or so after the event, you'll be sent a survey via email asking you for your feedback on your experience with this event today - it's designed to take less than two minutes to complete, and it helps us to understand how to wisely invest your time in future events. Your feedback is greatly appreciated. If you are applying for continuing education credit, completions of the surveys are mandatory as per your state boards and bars. 6 secret words (3 for each credit hour) will be given throughout the presentation. We will ask you to fill these words into the survey as proof of your attendance. Please stay tuned for the secret word. Speakers, I will be giving out the secret words at randomly selected times. I may have to break into your presentation briefly to read 3 September 23, 2014 the secret word. Pardon the interruption.
- 4. 4 September 23, 2014 Welcome to the Knowledge Group Unlimited Subscription Programs. We have Two Options Available for You: FREE UNLIMITED: This program is free of charge with no further costs or obligations. It includes: Unlimited access to over 15,000 pages of course material from all Knowledge Group Webcasts. Subscribers to this program can download any slides, white papers, or supplemental material covered during all live webcasts. 50% discount for purchase of all Live webcasts and downloaded recordings. PAID UNLIMITED: Our most comprehensive and cost-effective plan, for a one-time fee: Access to all LIVE Webcasts (Normally $199 to $349 for each event without a subscription). Including: Bring-a-Friend – Invite a client or associate outside your firm to attend for FREE. Sign up for as many webcasts as you wish. Access to all of Recorded/Archived Events & Course Material includes 1,500+ hours of audio material (Normally $299 for each event without a subscription). Free CLE/CPE/CE Processing (Normally $49 Per Course without a subscription). Access to over 15,000 pages of course material from Knowledge Group Webcasts. Ability to invite a guest of your choice to attend any live webcast Free of charge (Exclusive benefit only available for PAID UNLIMITED subscribers). 6 Month Subscription is $299 with No Additional Fees Other options are available. Special Offer: Sign up today and add 2 of your colleagues to your plan for free Check the “Triple Play” box on the sign-up sheet contained in the link below. https://gkc.memberclicks.net/index.php?option=com_mc&view=mc&mcid=form_157964
- 5. 5 September 23, 2014 Knowledge Group UNLIMITED PAID Subscription Programs Pricing: Individual Subscription Fees: (2 Options) Semi-Annual: $299 one-time fee for a 6 month subscription with unlimited access to all webcasts, recordings, and materials. Annual: $499 one-time fee for a 12 month unlimited subscription with unlimited access to all webcasts, recordings, and materials. Group plans are available. See the registration form for details. Best ways to sign up: 1. Fill out the sign up form attached to the post conference survey email. 2. Sign up online by clicking the link contained in the post conference survey email. 3. Click the link below or the one we just posted in the chat window to the right. https://gkc.memberclicks.net/index.php?option=com_mc&view=mc&mcid=form_157964 Discounts: Enroll today and you will be eligible for the “Triple Play” program and 3% off if you pay by credit card. Also we will waive the $49 CLE/CPE processing fee for today’s conference. See the form attached to the post conference survey email for details. Questions: Send an email to: info@knowledgecongress.org with “Unlimited” in the subject.
- 6. Partner Firms: 6 September 23, 2014 US Department of Homeland Security For companies that require the highest caliber of legal expertise coupled with a responsive and results driven approach, Carr McClellan is the boutique California business and business litigation law firm offering top-tier expertise and a full range of legal services. Carr McClellan serves both public and private companies, staying focused on the business objectives while giving clear advice and maintaining a flexible and practical approach to solving our clients’ business and legal matters. We remain deeply engaged in our clients’ businesses, tackling every issue with energy and initiative and we offer advice and solutions that work in the real world.
- 7. Partner Firms: 7 September 23, 2014 Walker Wilcox Matousek LLP, a Chicago-based law firm with offices in Houston, Texas, is at the forefront of the dynamic area of privacy law. WWM counsels clients on coverage for privacy risks under privacy, technology, first party, third party CGL policies and reinsurance contracts. WWM has been involved with privacy risks involving law firms, hospitals, financial institutions, retail, non-profit organizations, municipalities and schools. Headquartered in Houston, Texas, HCC Insurance Holdings, Inc. is a leading specialty insurer with offices in the United States, the United Kingdom, Spain and Ireland. As of March 31, 2014, HCC had assets of $10.6 billion and shareholders' equity of $3.8 billion. HCC's major domestic and international insurance companies have financial strength ratings of "AA (Very Strong)" from Standard & Poor's Corporation, "A+ (Superior)" from A.M. Best Company, Inc., "AA (Very Strong)" from Fitch Ratings, and "A1 (Good Security)" from Moody's Investors Service, Inc. For more information about HCC, please visit http://www.hcc.com. About HCC Specialty Headquartered in Wakefield, Massachusetts, HCC Specialty is among the industry’s leading managing underwriters of innovative specialty insurance products, including: high limit disability, professional liability, public entity, crisis management, contingency, DIC, prize indemnity and special program business. HCC Specialty, a division of HCC Insurance Holdings, Inc., is comprised of HCC Specialty Underwriters, Inc., Professional Indemnity Agency, Inc., G.B. Kenrick & Associates, Inc. dba Kenrick Corporation, InsPro Corporation and HCC Public Risk. For more information please visit http://www.hcc.com/specialty
- 8. Partner Firm: 8 September 23, 2014 CRC was founded in 1982 and specializes in Property, Casualty, and Professional risks. CRC’s extensive market experience allows it to draw on a wide range of resources from across the country and around the world. Created through the combination of CRC and Crump in April 2012, the new CRC Wholesale Group expanded to 1,800 employees and 50 offices nationwide. CRC’s Professional Liability Department - CRC-PRO - is a mainstay leader in Surplus Lines Market placement and innovation.
- 9. Brief Speaker Bios: Tom Finan Tom Finan is a Senior Cybersecurity Strategist and Counsel with the Department of Homeland Security’s National Protection and Programs Directorate, NPPD, where he leads work on cybersecurity insurance and cyber risk management in support of implementation of Executive Order 13636, “Improving Critical Infrastructure Cybersecurity.” Tom established DHS’ Cybersecurity Insurance webpage, accessible through the search engine of your choice, which includes a series of readout reports that describe DHS’ efforts in these areas. Previously, Tom led the effort to develop a resiliency-focused risk analysis and modeling office for NPPD that examines both cyber and physical threats to critical infrastructures, systems, and the public. Prior to his arrival at DHS, he served as the Staff Director and Counsel for the Subcommittee on Intelligence, Information Sharing and Terrorism Risk Assessment with the U.S. House Committee on Homeland Security where he advised the Subcommittee Chair, Congresswoman Jane Harman. Tom previously worked as an attorney for the FBI and in private litigation practice. 9 September 23, 2014 Helen A. Christakos Helen is an experienced business lawyer who represents clients in commercial transactions involving cutting edge intellectual property (IP) and technology issues. She brings a practical, business-oriented approach to advising companies ranging from global public companies to emerging start-up ventures in developing, licensing, selling, acquiring, protecting and commercially exploiting intellectual property and technology assets. She also devotes a significant portion of her practice to advising clients in a wide variety of industries on privacy, data security and ecommerce matters. Helen works with companies to assess their legal obligations and risks and helps design and implement practical, cost-effective plans for mitigating such risks. Helen conducts numerous CLE presentations to update in-house counsel on changes in privacy and data security law.
- 10. Brief Speaker Bios: Celeste M. King Celeste’s experience is with privacy risks and insurance. She advises insurers and reinsurers on coverage for privacy risks and breaches involving first and third party CGL policies, drafts policies and underwriting guidelines and prepares breach response strategies. Celeste counsels clients on state and federal regulations involving privacy laws, developments in case law and emerging issues such as standing to sue and recovery of reputational damages. She regularly deals with privacy risks to industries such as health care, legal and other professions, financial institutions, retail, insurance agents, public entities, education and energy. Celeste is also an experienced reinsurance lawyer, counseling clients on treaty and facultative risks and representing clients in reinsurance litigation and arbitration. 10 September 23, 2014 Brook Dutcher Brook Dutcher is Specialty Underwriting Manager-Technology E & O/Cyber Insurance product manager with HCC Specialty in New York. Brook focuses on new product development, product growth and strategy for the company. Previously he was the Technology E & O/Cyber Insurance product manager for NAS Insurance in California. He underwrote various lines and programs with Axis Insurance and with ACE Westchester in Atlanta. Prior to his career in insurance, Brook worked extensively in banking.
- 11. Brief Speaker Bios: Clay Segrest Mr. Segrest is a wholesale broker for CRC Insurance Services, Inc. specializing in Professional Liability, Executive Risk/Management Liability, and Network Security & Privacy Liability. He has played an instrumental role in his company’s efforts to expand its presence and influence in the Cyber Security & Privacy Liability marketplace. He has lectured the Alabama Independent Insurance Agents Association on this topic and he has helped lead CRC’s commitment to the growth and development of Cyber Liability products for producers and their clientele. As demand for Cyber coverage increases, CRC continues to provide complex risk solutions for insured’s realizing the magnitude of the exposure. Mr. Segrest received his Masters of Business Administration Degree from the University of Alabama at Birmingham and his undergraduate degree from Birmingham-Southern College. 11 ► For more information about the speakers, you can visit: http://theknowledgegroup.org/event_name/cyber-liability-insurance-an-essential-and-urgently-needed-business-investment/ September 23, 2014
- 12. Cyber Liability Insurance is a relatively new product that is developing rapidly due to increasing frequency and sophistication of cyber-attacks. Stricter regulation and enforcement of cyber crime are making purchase of Cyber Liability & Data Risk Insurance a necessity for many companies. Experian Inc. reports that almost 70% of business owners have yet to purchase some sort of insurance against cyber attack even though many business owners know cyber attack is a serious business risk. Many companies face significant costs from litigation following cyber attacks and even face the prospect of bankruptcy. In fact, The Gartner Group reports that 40% of all businesses experiencing data breaches are out of business within 6 months and 51% end business within two years following such cyber attacks. In this webinar, experts in the fields of cyber crime, cyber crime regulation and enforcement, insurance, cyber law, and network systems security will explain the risks, the types of insurance, and why it is increasingly essential to purchase such insurance. Special topics for discussion include: • Cyber Security Insurance Laws and Regulations • Cyber Liability Market and Claims Trends • Assessing Cyber Liability and Risks: Breach Litigation Issues • Cyber Insurance Types and Coverage Needs • Cyber Insurance Policies De-mystified • Subrogation: Vendor and Business Partner Liability Claims • Benefits of International Vulnerability Purchase Program 12 September 23, 2014
- 13. Featured Speakers: 13 September 23, 2014 SEGMENT 1: Tom Finan Senior Cybersecurity Strategist and Counsel US Department of Homeland Security SEGMENT 2: Helen A. Christakos Senior Counsel and Chair of the IP, Privacy & Data Security Group Carr, McClellan, Ingersoll, Thompson & Horn, PLC SEGMENT 3: Celeste M. King Founding Partner Walker Wilcox Matousek LLP SEGMENT 4: Brook Dutcher Underwriting Manager HCC Insurance Holdings, Inc. SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc.
- 14. Introduction Tom Finan is a Senior Cybersecurity Strategist and Counsel with the Department of Homeland Security’s National Protection and Programs Directorate, NPPD, where he leads work on cybersecurity insurance and cyber risk management in support of implementation of Executive Order 13636, “Improving Critical Infrastructure Cybersecurity.” Tom established DHS’ Cybersecurity Insurance webpage, accessible through the search engine of your choice, which includes a series of readout reports that describe DHS’ efforts in these areas. Previously, Tom led the effort to develop a resiliency-focused risk analysis and modeling office for NPPD that examines both cyber and physical threats to critical infrastructures, systems, and the public. Prior to his arrival at DHS, he served as the Staff Director and Counsel for the Subcommittee on Intelligence, Information Sharing and Terrorism Risk Assessment with the U.S. House Committee on Homeland Security where he advised the Subcommittee Chair, Congresswoman Jane Harman. Tom previously worked as an attorney for the FBI and in private litigation practice. 14 September 23, 2014 SEGMENT 1: Tom Finan Senior Cybersecurity Strategist and Counsel US Department of Homeland Security
- 15. Cybersecurity Insurance: DHS/NPPD Workshop Series Cyber Liability Insurance Webcast 15 September 23, 2014 SEGMENT 1: Tom Finan Senior Cybersecurity Strategist and Counsel US Department of Homeland Security
- 16. Strategic Background • To what extent can the cybersecurity insurance market offer relevant coverage at reasonable prices in return for an insured’s adoption of cyber risk controls and procedures that improve its risk posture? • Fire insurance carriers require sprinkler and other fire suppression systems as conditions for coverage. • Cybersecurity insurance what comparable risk controls and processes apply to cyber? 16 September 23, 2014 SEGMENT 1: Tom Finan Senior Cybersecurity Strategist and Counsel US Department of Homeland Security
- 17. Strategic Background • The third-party cybersecurity insurance market covers losses that a company causes to third parties, typically costs arising from a data breach (e.g., monetary damages arising from privacy and network security claims, some civil fines and penalties, attorneys’ fees). • The first-party cybersecurity insurance market covers a company’s own, direct losses from a cyber incident (e.g., lost profits, loss of intellectual property, loss of reputation, extraordinary costs associated with reconstituting damaged data and systems). 17 September 23, 2014 SEGMENT 1: Tom Finan Senior Cybersecurity Strategist and Counsel US Department of Homeland Security
- 18. Strategic Background • Four DHS/NPPD workshops since October 2012 have convened key stakeholders to engage on this topic. • Participants identified key challenges to a more robust first-party market that provides coverage for cyber-related critical infrastructure loss: Lack of actuarial data Lack of common cyber management best practices, metrics, and standards Lack of understanding of critical infrastructure “interconnectedness” and related domino effects that could result from a cyber attack Confusion about applicability of current insurance 18 September 23, 2014 SEGMENT 1: Tom Finan Senior Cybersecurity Strategist and Counsel US Department of Homeland Security
- 19. Strategic Background • Given these shortcomings, many carriers instead currently focus on the effectiveness of an organization’s cyber risk culture when assessing whether to provide cybersecurity insurance coverage and in what amounts. • The Four Pillars: Executive Leadership Education and Awareness Technology Relevant Information Sharing 19 September 23, 2014 SEGMENT 1: Tom Finan Senior Cybersecurity Strategist and Counsel US Department of Homeland Security
- 20. Strategic Background • Effective cyber risk culture takeaways: The business case for investing against cyber risk has not been made • Conveying cyber risk in terms of financial and reputational harm is difficult • True enterprise risk management (ERM) programs should address cyber risk Need for cost/benefit research on cybersecurity solutions Appropriate expectations for insurance in the cyber risk management space given competition and uncertainty concerns 20 September 23, 2014 SEGMENT 1: Tom Finan Senior Cybersecurity Strategist and Counsel US Department of Homeland Security
- 21. Strategic Background • Carriers reference three core questions when assessing each of these pillars and determining whether a company is a safe insurance “bet”: Does the company know what cyber incidents it has actually experienced based on its own data and reports from outside sources? Does the company know – through public sources and private conversation – what kinds of cyber incidents are happening to other companies like it? What informed cyber risk management investments is the company making based on this data? 21 September 23, 2014 SEGMENT 1: Tom Finan Senior Cybersecurity Strategist and Counsel US Department of Homeland Security
- 22. Strategic Background • EO 13636 – “Improving Critical Infrastructure Cybersecurity” • Impact of EO 13636 and NIST Cybersecurity Framework on cybersecurity insurance market: Risk management tool – common taxonomy that supports an enhanced underwriting roadmap Potential boon to market capacity – stemming the stand-alone trend Potential cost differentiator – Framework users and non-users 22 September 23, 2014 SEGMENT 1: Tom Finan Senior Cybersecurity Strategist and Counsel US Department of Homeland Security
- 23. Cybersecurity Insurance: Insurance Industry Working Session • In January 2014, the White House requested that DHS/NPPD lead a series of cybersecurity insurance incentive discussions to support EO 13636. • DHS/NPPD initiated the new discussions with an insurance industry-only working session in April 2014 centering on three topics: Cyber incident information sharing (creation of a cyber incident data repository) Cyber incident consequence analytics Cyber-inclusive ERM programs 23 September 23, 2014 SEGMENT 1: Tom Finan Senior Cybersecurity Strategist and Counsel US Department of Homeland Security
- 24. DHS Cybersecurity Insurance Webpage: http://www.dhs.gov/publication/cybersecurity-insurance. 24 September 23, 2014 SEGMENT 1: Tom Finan Senior Cybersecurity Strategist and Counsel US Department of Homeland Security
- 25. Introduction Helen is an experienced business lawyer who represents clients in commercial transactions involving cutting edge intellectual property (IP) and technology issues. She brings a practical, business-oriented approach to advising companies ranging from global public companies to emerging start-up ventures in developing, licensing, selling, acquiring, protecting and commercially exploiting intellectual property and technology assets. She also devotes a significant portion of her practice to advising clients in a wide variety of industries on privacy, data security and ecommerce matters. Helen works with companies to assess their legal obligations and risks and helps design and implement practical, cost-effective plans for mitigating such risks. Helen conducts numerous CLE presentations to update in-house counsel on changes in privacy and data security law. In addition to her law practice, Helen is an Adjunct Professor at Santa Clara University School of Law, where she teaches J.D. and LL.M. level classes in Technology and Intellectual Property Licensing. 25 September 23, 2014 SEGMENT 2: Helen A. Christakos Senior Counsel and Chair of the IP, Privacy & Data Security Group Carr, McClellan, Ingersoll, Thompson & Horn, PLC
- 26. State Data Security Breach Notification Laws 1. What do they cover? • Unencrypted personal information • Personal Information generally includes first name/first initial and last name in combination with: i. SS Number ii. Drivers License Number iii. Financial Account Number + code iv. Credit Card Number + code v. Debit Card Number + code 2. What is required in the event of a breach? • Requirements differ from state to state • Remedies differ from state to state 26 September 23, 2014 SEGMENT 2: Helen A. Christakos Senior Counsel and Chair of the IP, Privacy & Data Security Group Carr, McClellan, Ingersoll, Thompson & Horn, PLC
- 27. Amendment to California’s Data Security Breach Notification Law 1. Went into effect January 1, 2014 2. Law now covers on-line accounts 3. Electronic notice may now be given in certain circumstances 27 September 23, 2014 SEGMENT 2: Helen A. Christakos Senior Counsel and Chair of the IP, Privacy & Data Security Group Carr, McClellan, Ingersoll, Thompson & Horn, PLC
- 28. What should your Cyber Insurance Policies Cover 1. Both first-party and third-party risks 2. Unencrypted devices 3. Data breaches caused by third parties 4. Data transmissions outside the US 5. PCI liability (if applicable) 28 September 23, 2014 SEGMENT 2: Helen A. Christakos Senior Counsel and Chair of the IP, Privacy & Data Security Group Carr, McClellan, Ingersoll, Thompson & Horn, PLC
- 29. Introduction Celeste’s experience is with privacy risks and insurance. She advises insurers and reinsurers on coverage for privacy risks and breaches involving first and third party CGL policies, drafts policies and underwriting guidelines and prepares breach response strategies. Celeste counsels clients on state and federal regulations involving privacy laws, developments in case law and emerging issues such as standing to sue and recovery of reputational damages. She regularly deals with privacy risks to industries such as health care, legal and other professions, financial institutions, retail, insurance agents, public entities, education and energy. Celeste is also an experienced reinsurance lawyer, counseling clients on treaty and facultative risks and representing clients in reinsurance litigation and arbitration. Celeste is licensed in Illinois and District of Columbia and is AV Rated by Martindale-Hubbell. 29 September 23, 2014 SEGMENT 3: Celeste M. King Founding Partner Walker Wilcox Matousek LLP
- 30. Insurance For Cyber Risks 30 September 23, 2014 SEGMENT 3: Celeste M. King Founding Partner Walker Wilcox Matousek LLP
- 31. Know The Insured’s Risk - Federal and State Regulations - International Considerations - Industry Standards (e.g. PCIC) - Professional Regulatory Agencies - Contracts-Vendor Management - Reputation 31 September 23, 2014 SEGMENT 3: Celeste M. King Founding Partner Walker Wilcox Matousek LLP
- 32. Know The Coverage Already In Place •CGL Coverage -New ISO Exclusion •First Party Coverage •Directors and Officers Coverage •Professional Liability 32 September 23, 2014 SEGMENT 3: Celeste M. King Founding Partner Walker Wilcox Matousek LLP
- 33. Know The Coverage Needed • What are the Maximum Limits • Sublimits • Crisis Management (Notification, PR) • Regulatory Fines • Business Interruption • Defense Expenses • Cyber Extortion 33 September 23, 2014 SEGMENT 3: Celeste M. King Founding Partner Walker Wilcox Matousek LLP
- 34. Cyber Coverage Issues • Terrorism or Hacktivism or Cyber War • Unauthorized collection of data • Contractual liability • Company-wide training • Paper/non-electronic breaches covered • Confidentiality Agreements and NDAs • Cloud • International laws 34 September 23, 2014 SEGMENT 3: Celeste M. King Founding Partner Walker Wilcox Matousek LLP
- 35. Keep Current With Changes • Wordings Change With Technology –”internet of things” - bodily injury (e.g. medical devices) • Court opinions interpreting wordings • Changes in state and federal laws • Competition in the marketplace 35 September 23, 2014 SEGMENT 3: Celeste M. King Founding Partner Walker Wilcox Matousek LLP
- 36. Challenges to Insurers and Reinsurers • Uncertainty of the legal framework • Cyber is a business issue, not only IT • Pricing the risk • Keeping the privilege • Selecting the experts: who and when • Aggregation of multiple losses 36 September 23, 2014 SEGMENT 3: Celeste M. King Founding Partner Walker Wilcox Matousek LLP
- 37. 37 CLE PROCESSING The Knowledge Group offers complete CLE processing solutions for your webcasts and land events. This comprehensive service includes everything you need to offer CLE credit at your conference: September 23, 2014 Complete end-to-end CLE credit Solutions Setting up your marketing collateral properly. Completing and filing all of the applications to the state bar. Guidance on how to structure content meet course material requirements for the state Bars. Sign up forms to be used to check & confirm attendance at your event. Issuing official Certificates of Attendance for credit to attendees. Obtaining CLE credit varies from state to state and the rules can be complex. The Knowledge Group will help you navigate the complexities via complete cost effective CLE solutions for your conferences. Most CLE processing plans are just $499 plus filing fees and postage. To learn more email us at info@knowledgecongress.org or CALL 646-202-9344
- 38. 38 September 23, 2014 PRIVATE LABEL PROGRAM & INTERNAL TRAINING The Knowledge Group provides complete private label webcasts and in-house training solutions. Developing and executing webcasts can be a huge logistical nightmare. There are a lot of moving parts and devolving a program that is executed smoothly and cost effectively can prove to be a significant challenge for companies who do not produce events on a regular basis. Live events require a high level of proficiency in order to execute proficiently. Our producers will plan and develop your webcast for you and our webcast technicians will execute your live event with expert precision. We have produced over 1000 live webcasts. Put our vast expertise to work for you. Let us develop a professional webcast for your firm that will impress all your clients and internal stakeholders. Private Label Programs Include: Complete Project Management Topic Development Recruitment of Speakers (Or you can use your own) Marketing Material Design PR Campaign Marketing Campaign Event Webpage Design Slides: Design and Content Development Speaker coordination: Arranging & Executing Calls, Coordinating Slides & Content Attendee Registration Complete LIVE Event Management for Speaker and Attendees including: o Technical Support o Event Moderator o Running the Live event (All Aspects) o Multiple Technical Back-ups & Redundancies to Ensure a Perfect Live Event o Webcast Recording (MP3 Audio & MP4 Video) o Post Webcast Performance Survey CLE and CPE Processing Private Label Programs Start at just $999
- 39. 39 September 23, 2014 RESEARCH & BUSINESS PROCESS OUTSOURCING The Knowledge Group specializes in highly focused and intelligent market and topic research. Outsource your research projects and business processes to our team of experts. Normally we can run programs for less than 50% of what it would cost you to do it in-house. Here are some ideal uses for our services: Market Research and Production o List Research (Prospects, Clients, Market Evaluation, Sales Lists, Surveys) o Design of Electronic Marketing Collateral o Executing Online Marketing Campaigns (Direct Email, PR Campaigns) o Website Design o Social Media Analysis & Research o Research Companies & Produce Reports o Research for Cases o Specialized Research Projects eSales (Electronic Inside Sales – Email and Online) o Sales Leads Development o eSales Campaigns Inside Sales people will prospect for leased, contact them and coordinate with your sales team to follow up. Our Inside eSales reps specialize in developing leads for big-ticket enterprise level products and services. o Electronic Database Building – Comprehensive service which includes development of sales leads, contacting clients, scoring leads, adding notes and transferring the entire data set to you for your internal sales reps. eCustomer Service (Electronic Inside Sales – Email and Online) o Real-Time Customer Service for Your clients Online Chat Email o Follow-Up Customer Service Responds to emails Conducts Research Replies Back to Your Customer Please note these are just a few ways our experts can help with your Business Process Outsourcing needs. If you have a project not specifically listed above please contact us to see if we can help.
- 40. Introduction Brook Dutcher is Specialty Underwriting Manager-Technology E & O/Cyber Insurance product manager with HCC Specialty in New York. Brook focuses on new product development, product growth and strategy for the company. Previously he was the Technology E & O/Cyber Insurance product manager for NAS Insurance in California. He underwrote various lines and programs with Axis Insurance and with ACE Westchester in Atlanta. Prior to his career in insurance, Brook worked extensively in banking. 40 September 23, 2014 SEGMENT 4: Brook Dutcher Underwriting Manager HCC Insurance Holdings, Inc.
- 41. The Value of Cyber Insurance An overview from a carriers perspective 41 September 23, 2014 SEGMENT 4: Brook Dutcher Underwriting Manager HCC Insurance Holdings, Inc.
- 42. Coverage Development 42 September 23, 2014 SEGMENT 4: Brook Dutcher Underwriting Manager HCC Insurance Holdings, Inc. Breach Response and Crisis Management as stand alone coverage Technology E & O including 3rd party Privacy & Security and eventually 1st party coverages Technology E & O Products Specialized custom liability coverage
- 43. Diverse approaches to the coverage 43 September 23, 2014 SEGMENT 4: Brook Dutcher Underwriting Manager HCC Insurance Holdings, Inc. Breach response with coverage for the actions of the board, including the CIO D & O MPL Breach response coverage with 3rd party coverage for the performance of services Technology E & O 1st and 3rd party coverages Financial Lines Breach response products to address computer crime and fraud Media Cyber insurance coupled with Media related coverage for IP, Content and related services Catastrophic Large Limit Breach Response Products
- 44. Why include cyber in my portfolio? 44 September 23, 2014 SEGMENT 4: Brook Dutcher Underwriting Manager HCC Insurance Holdings, Inc. Cost of doing business Increase in direct and indirect costs Costs of notification required, Cost of defense, forensics, regulatory action Cyber insurance addresses contemporary business exposures in a unique fashion Clearer boundaries are emerging and being defined between lines of coverage Coverage is becoming a necessity The US accounts for more data incidents than any other country. Two states in the US account for the majority of those incidents. The present interpretation of market conditions indicate all businesses will have some kind of incident.
- 45. Business Posture 45 September 23, 2014 SEGMENT 4: Brook Dutcher Underwriting Manager HCC Insurance Holdings, Inc. Most businesses have been reactionary to cyber related incidents despite efforts to be proactive. Inherent flaws in the fundamentals of programming have forced businesses to re-evaluate prioritization of exposures and value. Measurable effects to share value and the security of C-Suite positions have forced organizations to review business methodology.
- 46. The Shift from Reactive to Proactive Posture 46 September 23, 2014 SEGMENT 4: Brook Dutcher Underwriting Manager HCC Insurance Holdings, Inc. Human Error Global Exchange of Information State Sponsored Activity Political Activism Criminal Enterprise Quarrelsome Clients Constricting Regulatory Guidelines • Emerging Case Law • State and Federal AG • Speculative Punitive Damages • Monitization of IP and PII • Sharing of information
- 47. A culture of accountability 47 September 23, 2014 SEGMENT 4: Brook Dutcher Underwriting Manager HCC Insurance Holdings, Inc. Data now shows companies with a strong security posture can reduce costs per record significantly in the event of a breach Companies are compelled to retain customers as organizations with a higher customer turn over and churn rate were more likely to experience higher breach costs. Costs of notification are significantly higher in the US causing a re-evaluation of costs to conduct business in the US and the exposures of conducting business abroad. US also experiences the highest costs associated with lost business in the event of a breach inspiring businesses to adhere to higher standards
- 48. A culture of accountability 48 September 23, 2014 SEGMENT 4: Brook Dutcher Underwriting Manager HCC Insurance Holdings, Inc. Compliance Stability Corporate Culture of Accountability Written Procedures Continuity of Operations Vetting of Contractors Incident Response Plan Minimal Down Time Proactive Protocol for Vulnerability Management
- 49. Global Market Place 49 September 23, 2014 SEGMENT 4: Brook Dutcher Underwriting Manager HCC Insurance Holdings, Inc. Focus of coverage tends to vary from region to region. The issues revolving around ownership of data and the responsibility of data continue to move to the forefront. U.S. represents, by far, the greatest number of incidents, the largest amounts of data per incident and the greatest costs per incident. International groups are collaborating on standards. Japan to release new ISO guidelines for Cloud Utility The international legal community is becoming more fluent in notification responsibilities from one nation to another
- 50. Access to Solutions 50 September 23, 2014 SEGMENT 4: Brook Dutcher Underwriting Manager HCC Insurance Holdings, Inc. Pre-emptive screening or auditing Experienced breach coach Access to forensic service providers Call centers at your disposal Experienced Claim Handling Forensic accountants to quantify interruption costs Public Relations Firms to put out media firestorms
- 51. A few parting words 51 September 23, 2014 SEGMENT 4: Brook Dutcher Underwriting Manager HCC Insurance Holdings, Inc. The market will continue to grow and evolve The exposure will continue to grow and evolve. For more information on HCC Specialty visit: http://www.hcc.com/specialty/
- 52. Introduction Mr. Segrest is a wholesale broker for CRC Insurance Services, Inc. specializing in Professional Liability, Executive Risk/Management Liability, and Network Security & Privacy Liability. He has played an instrumental role in his company’s efforts to expand its presence and influence in the Cyber Security & Privacy Liability marketplace. He has lectured the Alabama Independent Insurance Agents Association on this topic and he has helped lead CRC’s commitment to the growth and development of Cyber Liability products for producers and their clientele. As demand for Cyber coverage increases, CRC continues to provide complex risk solutions for insured’s realizing the magnitude of the exposure. Mr. Segrest received his Masters of Business Administration Degree from the University of Alabama at Birmingham and his undergraduate degree from Birmingham-Southern College. 52 September 23, 2014 SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc.
- 53. Expanding Threats • Increased sophistication of criminal cyber-attacks • Insecure websites, databases and health information exchanges that are highly vulnerable to insider and outsider threats. • Employee increased use of personal unsecured mobile devices (smart phones, laptops, i-Pads) to connect to company networks or enterprise systems • Regulatory Compliance • Cloud Services (40% of organizations use the cloud heavily) -- Common Applications & Services: – Backup and storage – Productivity – File-sharing and collaboration – Accounting and payroll data – Medical records and billing 53 September 23, 2014 SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc.
- 54. Defining Your Perimeter 54 September 23, 2014 SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc. Customers Contracted Business Partners Employees Management
- 55. Claim Payouts by Type of Cost 145 Data Breach Claims -- 88 Claims Payouts -- $84M Payout (N=88) 55 September 23, 2014 SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc. 50% 36% 13% 1% Crisis Services Legal Defense Legal Settlement PCI Fines and Regulatory Fines Smallest Claim Payout: $2,560 Largest Claim Payout: $20,000,000 Average Payout: $954,000
- 56. Crisis Service Costs (N=66) 56 September 23, 2014 SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc. 50% 36% 13% 1% Crisis Services Legal Defense Legal Settlement PCI Fines and Regulatory Fines 50 42 33 53 60 50 40 30 20 10 0 Forensics Notification Credit Monitoring Legal Guidance
- 57. 57 September 23, 2014 SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc. Legal Defense & Settlement Costs (N=40) 50% 36% 13% 1% Crisis Services Legal Defense Legal Settlement 36 29 10 40 35 30 25 20 15 10 5 0 Defense Settlement Both
- 58. 58 September 23, 2014 SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc. 16% 12% 1% 12% 27% 29% 2% 1% Credit/Debit Card Financial N/A Other PHI PII Trade Secrets Unknown Percentage of Claims by Data Type (N=140)
- 59. Percentage of Claims by Cause of Loss 59 September 23, 2014 SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc. (N=140) 19% 3% 21% 10% 8% 5% 8% 12% 4% 6% 4% Hacker Improper data collection Lost/stolen laptop or device Malware/Virus Other Paper records Rogue employee Staff mistake System glitch Theft Third-party vendor
- 60. 60 September 23, 2014 SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc. Percentage of Claims by Business Sector (N=140) 7% 3% 15% 29% 3% 13% 11% 3% 6% 8% 2% Education Entertainment Financial Services Healthcare Hospitality Non‐Profit Other/Unknown Professional Services Retail Technology Telecommunications
- 61. 61 September 23, 2014 SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc. Percentage of Claims by Revenue Size (N=140) 22% 13% 23% 12% 1% 4% 25% Nano‐Cap (< $50M) Micro‐Cap ($50M‐$300M) Small‐Cap ($300M‐$2B) Mid‐Cap ($2B‐$10B) Mega‐Cap (> $100B) Large‐Cap ($10B‐$100B) Unknown
- 62. Breaking the Buyer Barrier Sales Challenges • The Long Cyber Sale Cycle & producer endurance • Realizing the magnitude of the exposure and the value of the products available – Asking the right questions to the right people – Connecting with the IT Department • Product education & coverage expertise – Value added services • Financial Constraints – Insurance Budget 62 September 23, 2014 SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc.
- 63. Breaking the Buyer Barrier Logistics of Obtaining Cyber Coverage • Application Process -- providing a picture of the overall network perimeter • Underwriting Community Concerns -- slowly requiring more information before finalizing terms & conditions • Underwriting Submission Information & Rating – Class -- Type of business or service provided – Revenue -- Revenues vs Record Count. What is a record? – Amount of information at risk / Number and size of records / Nature of records • Answering Cyber Questions 63 September 23, 2014 SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc.
- 64. Cyber Progress 64 September 23, 2014 SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc. Discovering a Data Breach Increased Awareness & Education Securing Devices Valued Partner & Trusted Business Advisor
- 65. Q&A: ► You may ask a question at anytime throughout the presentation today. Simply click on the question mark icon located on the floating tool bar on the bottom right side of your screen. Type your question in the box that appears and click send. ► Questions will be answered in the order they are received. 65 September 23, 2014 SEGMENT 1: Tom Finan Senior Cybersecurity Strategist and Counsel US Department of Homeland Security SEGMENT 2: Helen A. Christakos Senior Counsel and Chair of the IP, Privacy & Data Security Group Carr, McClellan, Ingersoll, Thompson & Horn, PLC SEGMENT 3: Celeste M. King Founding Partner Walker Wilcox Matousek LLP SEGMENT 4: Brook Dutcher Underwriting Manager HCC Insurance Holdings, Inc. SEGMENT 5: Clay Segrest Professional Liability Broker CRC Insurance Services, Inc.
- 66. 66 September 23, 2014 Welcome to the Knowledge Group Unlimited Subscription Programs. We have Two Options Available for You: FREE UNLIMITED: This program is free of charge with no further costs or obligations. It includes: Unlimited access to over 15,000 pages of course material from all Knowledge Group Webcasts. Subscribers to this program can download any slides, white papers, or supplemental material covered during all live webcasts. 50% discount for purchase of all Live webcasts and downloaded recordings. PAID UNLIMITED: Our most comprehensive and cost-effective plan, for a one-time fee: Access to all LIVE Webcasts (Normally $199 to $349 for each event without a subscription). Including: Bring-a-Friend – Invite a client or associate outside your firm to attend for FREE. Sign up for as many webcasts as you wish. Access to all of Recorded/Archived Events & Course Material includes 1,500+ hours of audio material (Normally $299 for each event without a subscription). Free CLE/CPE/CE Processing3 (Normally $49 Per Course without a subscription). Access to over 15,000 pages of course material from Knowledge Group Webcasts. Ability to invite a guest of your choice to attend any live webcast Free of charge. (Exclusive benefit only available for PAID UNLIMITED subscribers.) 6 Month Subscription is $299 with No Additional Fees. Other options are available. Special Offer: Sign up today and add 2 of your colleagues to your plan for free. Check the “Triple Play” box on the sign-up sheet contained in the link below. https://gkc.memberclicks.net/index.php?option=com_mc&view=mc&mcid=form_157964
- 67. 67 September 23, 2014 Knowledge Group UNLIMITED PAID Subscription Programs Pricing: Individual Subscription Fees: (2 Options) Semi-Annual: $299 one-time fee for a 6 month subscription with unlimited access to all webcasts, recordings, and materials. Annual: $499 one-time fee for a 12 month unlimited subscription with unlimited access to all webcasts, recordings, and materials. Group plans are available. See the registration form for details. Best ways to sign up: 1. Fill out the sign up form attached to the post conference survey email. 2. Sign up online by clicking the link contained in the post conference survey email. 3. Click the link below or the one we just posted in the chat window to the right. https://gkc.memberclicks.net/index.php?option=com_mc&view=mc&mcid=form_157964 Discounts: Enroll today and you will be eligible for the “Triple Play” program and 3% off if you pay by credit card. Also we will waive the $49 CLE/CPE processing fee for today’s conference. See the form attached to the post conference survey email for details. Questions: Send an email to: info@knowledgecongress.org with “Unlimited” in the subject.
- 68. 68 September 23, 2014 ABOUT THE KNOWLEDGE GROUP, LLC. The Knowledge Group, LLC is an organization that produces live webcasts which examine regulatory changes and their impacts across a variety of industries. “We bring together the world's leading authorities and industry participants through informative two-hour webcasts to study the impact of changing regulations.” If you would like to be informed of other upcoming events, please click here. Disclaimer: The Knowledge Group, LLC is producing this event for information purposes only. We do not intend to provide or offer business advice. The contents of this event are based upon the opinions of our speakers. The Knowledge Group does not warrant their accuracy and completeness. The statements made by them are based on their independent opinions and does not necessarily reflect that of The Knowledge Group‘s views. In no event shall The Knowledge Group be liable to any person or business entity for any special, direct, indirect, punitive, incidental or consequential damages as a result of any information gathered from this webcast. Certain images and/or photos on this page are the copyrighted property of 123RF Limited, their Contributors or Licensed Partners and are being used with permission under license. These images and/or photos may not be copied or downloaded without permission from 123RF Limited
