TACOM 2014: Back To Basics
- 2. BACK TO BASICS FOR INFORMATION SECURITY Joel Cardella Director, Information Security Holcim US
- 3. Biographical Info • Joel Cardella • 20 years in Information Technology • Network Operations • Data Center • Telecommunications • Health Care • Manufacturing • Currently Regional Security Officer for multinational industrial manufacturing organization • Passionate evangelist of infosec
- 4. Security problems in the news
- 5. The (abbreviated) story of Mat
- 6. Who • Mat Honan is a digital journalist, writing for Wired, Gizmodo and a number of digital magazines • On August 3, 2012, hackers used simple social engineering to trick Amazon and Apple into providing information that would allow them to take over the AppleID of Wired reporter Mat Honan Name Last 4 of credit card on file Email address Billing address
- 7. What • Mat had the following happen • Gmail account compromised & deleted • Me.com email account compromised • Apple (icloud.com) ID compromised • Remote wipe of iPhone • Remote wipe of Macbook • Twitter account compromised • It was 10 minutes between when he noticed his iPhone being wiped and calling AppleCare • By then it was far too late – 30 minutes earlier the hack had occurred • 2 minutes later the hackers post on his hacked Twitter account
- 9. Why • Mat is a public figure so it’s expected you can find more info on him than a non-public figure • However, our hackers had only one thing in mind when they hacked his account – what do you think it was? • He had a 3 letter Twitter name (@mat) and they liked it and wanted to use it
- 10. Poor basic practices • While this hack was clever, Mat also observed poor basic security practices • “My Twitter account linked to my personal website, where they found my Gmail address.” • He re-used the same username/email name (and possibly password) • “If I had some other account aside from an Apple e-mail address, or had used two-factor authentication for Gmail, everything would have stopped [when the hackers accurately guessed that information].”
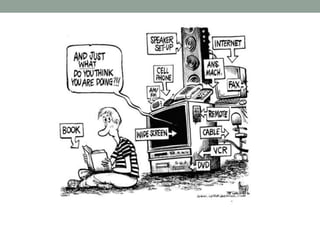
- 11. http://infospectives.me/2014/07/31/modifying-maslow-what-really-drives-your-infosec-needs-the-state-of-security/ Other controls Low Medium High Critical Basic security starts with foundations
- 12. http://infospectives.me/2014/07/31/modifying-maslow-what-really-drives-your-infosec-needs-the-state-of-security/ Buy latest hyped product Panic Pray Hope Procrastinate Unfortunately…
- 13. • “…if your roof has leaks, you fix the leaks in the roof before you remodel the house, right?” • John Pescatore, SANS http://www.techrepublic.com/blog/tech-decision-maker/it-security-fix-the-leaky- roof-before-remodeling-the-house/
- 14. Pareto principle • Aka the 80/20 rule • In anything, a few (20) are vital and many (80) are trivial • In security terms: focusing on 20% of your basics can address 80% of your risk
- 15. 3 key words
- 16. PERSONAL BASICS Part 1
- 17. Walls of separation • Build walls of separation between your online identities • Do not reuse usernames • Do not reuse email addresses • Do not reuse passwords • Separate work from home, bank from everything • Use password managers to help with this • Keepass (http://keepass.info/) • LastPass (https://lastpass.com/) • 1Password (https://agilebits.com/onepassword)
- 18. Strong passwords • Minimum complexity of Upper, Lower, Number & Symbol, plus spaces if you can • Passphrases are the best choice if available • Use spaces where you can, form “words” • Mis-spelling of words helps! • Minimum 10 characters – for now…
- 19. Rainbow tables guess passwords https://www.freerainbowtables.com/
- 20. Multifactor where available Something you know Something you have Strong authentication
- 21. Social media Whether or not you are out there, you are out there!
- 22. ENTERPRISE BASICS Part 2
- 24. The basics PREVENT DETECT RESPOND RECOVER
- 25. Risk Defined in Security Terms Threats increase risk Dealing with vulnerabilities reduces risk When a threat connects with a vulnerability, there is impact (Offense) (Defense) Likelihood Impact THREATS X VULNERABILITIES = RISK Reduces Risk Drives risk calculation Source: Dr Eric Cole, SANS
- 26. Critical security controls • Quick wins • Ways to monitor & measure • Easy way to speak to your business / create scorecard
- 27. Rapid approach to the basics • Application whitelisting (CSC 2/DSD 1) • Use of standard, secure system configurations (CSC 3) • Patch application software within 48 hours (CSC 4/DSD 2) • Patch system software within 48 hours (CSC 4/DSD 3) • Reduce number of users with administrative privileges (CSC 3 and 12/DSD 4) • DSD suggests these will fit into the Pareto principle and address 80% of your risks
- 28. BASICS IN DEPTH Part 3
- 29. Basic attack pattern of all intruders Inbound connection Open a port / start a service Outbound connection For basics, what can we focus on to mitigate this attack pattern?
- 30. Recon your network • What are your assets? • Hardware • Software • Are you aware of authorized vs unauthorized assets? • Can you tell when this changes? • ARE YOU SURE?
- 31. Recon – things TO DO • Create a standard user account • Login in from the outside and from the inside (both sides of your firewall) • Where can you go? What can you see? What do you have access to? • Do you understand what you are seeing? • Are you forgetting anything? Look for examples of what other breaches have occurred and what they have tried • Threat modeling works well here
- 32. Account management – WHAT TO ASK • What types of accounts exist in your enterprise? • Do you know who owns those accounts? • Do you know if those accounts are still valid? • If you have system or service accounts, do you know what they have access to (zones)? • ARE YOU SURE?
- 33. Account management – WHAT TO DO • Manage your accounts by policy and technical enforcement • Expire passwords/password complexity • Use ACLs to manage access to your systems • Restrict access within your zones • Enforce 2nd factor authentication for vendor/contractor access • For employees if you can! For everyone! • Inventory your accounts and their parameters • Know your vendors by their accounts
- 34. Controlled access – WHAT TO ASK • What systems can talk to each other? • Are they in different zones? Do they need to be? • Do your business people have access to information they do not need to do their jobs? • Do your administrators have more access than they need to do their jobs? • What about non-admins? • ARE YOU SURE?
- 35. Controlled access – WHAT TO DO • Access based on need to know/need to work • Classification scheme is needed for this • Establish a policy of access based on need to know/need to work • Establish approval mechanism for special exceptions • Talk to the business to find out what access they need, and create a Segregation of Duties (SoD) matrix • Enforce SoD through system constraints and involve the business in the SoD approvals
- 36. Vendor Account Network Segmentation Target PC Target PC Target PC Target PC Vendor Account Target PC Target PC Target PC Target PC V P N ARE YOU SURE? Account management in place Access is controlled to these resources Changes over time to firewall rules create holes A D V P N A D Changes to access control lists also create holes Our controls are in place … but are they working as designed? Recon + threat modeling
- 37. Two factor is a strong defense against external intrusion Vendor Account Target PC Target PC Target PC Target PC Systems allow account logins at the OS Internal firewalls have holes Scenario 2 – Vendor account has privileges escalated Vendor Account Target PC Target PC Target PC Target PC Systems allow account logins at the OS but only for privilege V P N A D 2nd factor challenge V P N A D 2nd factor challenge Internal firewalls have holes
- 38. Backup strategy –WHAT TO ASK • Do you have a backup strategy? • Is it documented? • Does it align with your business needs? • Backups cost money, time and resources • Do you back up more than you need? • Do you have resources to verify/restore backups? • Do you regularly test backups? • When was the last time you did and what were the results? • Did you document this? • ARE YOU SURE?
- 39. Backup strategy –WHAT TO DO • Create a policy for regular backups • Identify critical systems & backup frequency • If you have a DRD in place make sure it’s being adhered to • Document a Recovery Time Objective (RTO) and a Recovery Point Objective (RPO) for your backups • This aligns with disaster planning / BCP • Must be done in alignment with your business • VERIFY YOUR BACKUPS • This is not negotiable or avoidable!
- 40. Change management • Who approves your security changes? • Is this documented and reviewed periodically? • Who reviews your security changes for accuracy? • Who follows up to verify the changes are still accurate? • Document reasons for changes, approvals and mitigations • ARE YOU SURE?
- 41. Establish a governance calendar • The calendar contains your regular cadence of review activity • You can script reminders to the entities responsible for the review • SharePoint • Google scripts (Google calendar) • Work this activity into your existing processes so they get prioritized • Time box those activities! • Get SLAs/SLOs for teams on which you rely to perform these activities
- 42. Sample Governance Calendar Q1 Q2 Q3 Q4 Jan Feb Mar Apr May Jun Jul Aug Sep Oct Nov Dec DR Testing Recon Recon Backup testing Backup testing Backup testing AD review AD AD review review Mid year audit Operations Security Data Center Audit
- 43. Important Enterprise Infosec Lessons 1. There is no magic bullet – infosec is multi-layered and multi-disciplinary 2. Infosec will cost you time, money and resources – measure your value appropriately 3. Infosec is an active discipline; it requires care and feeding, you cannot install and forget 4. Time is the enemy of infosec; the longer it takes, the higher the risks 5. Infosec is a value add for your business, and it is up to you to show it – in many cases it IS the business 6. Infosec is not a department of “no.” Market yourself like a startup
- 44. Security basics put simply… • If you think technology can fix security, you don’t understand technology and you don’t understand security. • The root cause of a security incident is rarely about the technology and almost always about the implementation. • Humans will always be the weakest link in the security chain. Awareness will mitigate the vast majority of your security issues … spend time and money on educating everyone in your company about security.
- 46. Tools & references list • http://csc-hub.com/ - Ken Evan’s awesome 20 CSC site • http://technet.microsoft.com/en-us/ magazine/2007.02.activedirectory.aspx - AD rights delegation • http://sectools.org/ - List of pay and free network tools • http://www.poshsec.com/ - Powershell scripts that support the 20 CSC • http://www.asd.gov.au/infosec/top35mitigationstrategies.htm - Australian DSD Top 35 • http://www.counciloncybersecurity.com – Council on Cybersecurity • http://www.jwgoerlich.us/blogengine/post/2014/04/29/Update-on-Story- Driven-Security.aspx - J. Wolfgang Goerlich and Nick Jacob’s work on effective threat modeling • http://www.theguardian.com/commentisfree/2014/may/06/target-credit-card- data-hackers-retail-industry - Brian Kreb’s op-ed on the current state of the Target breach and some of the false pretense
- 47. Contact info • Joel Cardella • LinkedIn: https://www.linkedin.com/pub/joel-cardella/0/107/412 • Twitter: @JoelConverses or @jscardella • Email: jscardella@pobox.com • IRC: #misec on Freenode (joel_s_c)
Hinweis der Redaktion
- So let’s talk about how we in Security define risk. Threats increase our risk. Threats can be known issues (known OS / app bugs, patching). They can be unknown issues (zero days) The more we address vulnerabilities, the less risk we assume. When a threat and vulnerability meet, we have impact. Sometimes we can predict the impact and sometimes we cannot.
