Public-Key Protocols
- 1. Engineering Cryptographic Applications Day 3: Public Key Protocols David Evans University of Virginia www.cs.virginia.edu/evans Microstrategy Course 18 October 2013
- 2. Recap: Symmetric Encryption Alice Bob Ciphertext Plaintext AES AES Plaintext Insecure Channel Key Key Assuming we generate strong keys, use an appropriate cipher mode, and correctly implement a secure symmetric encryption primitive, we can securely encrypt long messages so even an adversary with $Quadrillions cannot learn anything interesting. Assumes a secret already shared between Alice and Bob. Amplifies that secret to send more data later. evans@virginia.edu Engineering Crypto Applications 1
- 3. Plan for Today Insecure Channel Secure Channel petitions.gov 1. Key Agreement Protocols 2. Solving the remote authentication problem Asymmetric Encryption, Public-Key Protocols evans@virginia.edu Engineering Crypto Applications 2
- 4. Key Agreement evans@virginia.edu Engineering Crypto Applications 3
- 5. Merkle’s Puzzles (1974) Asymmetric Key Agreement Ralph Merkle (born 1952) evans@virginia.edu Engineering Crypto Applications 4
- 6. Merkle’s Puzzles: Key Agreement Alice 1. Generate N random keys: k0, …, kn-1 2. For each, send Eki(“key #” + i) EE37(“key #” ++37) in random order k (“key #” 82) k E82 (“key #” + 22) k22 … evans@virginia.edu Engineering Crypto Applications 5
- 7. Merkle’s Puzzles: Key Agreement Alice 1. Generate N random keys: k0, …, kn-1 2. For each, send Eki(“key #” + i) EE37(“key #” ++37) in random order k (“key #” 82) k E82 (“key #” + 22) k22 … evans@virginia.edu Engineering Crypto Applications 6
- 8. Alice 1. Generate N random keys: k0, …, kn-1 2. For each, send Eki(“key #” + i) EE37(“key #” ++37) in random order k (“key #” 82) Bob k E82 (“key #” + 22) k22 … x 3. Randomly select one of the received messages. 4. Try all possible keys until finding kx that decrypts the message to “key #x” 5. Send x (in clear) to Alice Shared secret kx evans@virginia.edu Engineering Crypto Applications 7
- 9. Bob Alice Security Generate N random keys: k0, …, kn-1 2. For each, send Eki(“key #” + i) in random order 1. 3. 4. x 5. Randomly select one of the received messages. Try all possible keys until finding kx that decrypts the message to “key #x” Send x (in clear) to Alice Shared secret kx evans@virginia.edu Engineering Crypto Applications 8
- 10. Bob Alice Security Generate N random keys: k0, …, kn-1 2. For each, send Eki(“key #” + i) in random order 1. 3. 4. x 5. Randomly select one of the received messages. Try all possible keys until finding kx that decrypts the message to “key #x” Send x (in clear) to Alice Shared secret kx Suppose each key is 56 bits: Alice has to generate N keys and do N encryptions Bob has to do 256 max work to brute force Eve has to do ½N × 255 expected work So, if 296 is infeasible, N = 242 could work evans@virginia.edu Engineering Crypto Applications 9
- 11. Can we do better? CRYPTO 2009: Actually is impossible to do better! Any scheme like this, even with perfect primitives, can be broken by an adversary who can do N 2 encryptions (where Alice and Bob do N encryptions). To do better, we need some magic math! evans@virginia.edu Engineering Crypto Applications 10
- 12. Time for a Revolution! “We stand today on the brink of a revolution in cryptography. The development of cheap digital hardware has freed it from the design limitations of mechanical computing and brought the cost of high grade cryptographic devices down to where they can be used in such commercial applications as remote cash dispensers and computer terminals. In turn, such applications create a need for new types of cryptographic systems which minimize the necessity of secure key distribution channels and supply the equivalent of a written signature. At the same time, theoretical developments in information theory and computer science show promise of providing provably secure cryptosystems, changing this ancient art into a science.” Whit Diffie and Martin Hellman, November 1976. evans@virginia.edu Engineering Crypto Applications 11
- 13. Padlocked Boxes MSTR Alice evans@virginia.edu Engineering Crypto Applications 12
- 14. Padlocked Boxes EA(M) Alice’s Padlock Alice Alice’s Padlock Key evans@virginia.edu Engineering Crypto Applications 13
- 15. Padlocked Boxes Shady Sammy’s Slimy Shipping Service Alice Alice’s Padlock Key evans@virginia.edu Engineering Crypto Applications 14
- 16. Padlocked Boxes EB( EA(M)) Bob’s Padlock Alice Bob Alice’s Padlock Key Bob’s Padlock Key evans@virginia.edu Engineering Crypto Applications 15
- 17. Padlocked Boxes EB(EA(M)) Alice Bob Alice’s Padlock Key Bob’s Padlock Key evans@virginia.edu Engineering Crypto Applications 16
- 18. Padlocked Boxes DA(EB(EA(M))) = EB(M) Alice Bob Alice’s Padlock Key Bob’s Padlock Key evans@virginia.edu Engineering Crypto Applications 17
- 19. Padlocked Boxes EB(M) Alice Bob Bob’s Padlock Key evans@virginia.edu Engineering Crypto Applications 18
- 20. Padlocked Boxes MSTR Alice Bob Bob’s Padlock Key evans@virginia.edu Engineering Crypto Applications 19
- 21. “Padlocks” Key Agreement • We relied on: DA(EB(EA(M))) = EB(M) • Is this true for AES? No way! AES (and any strong symmetric primitive) must involve non-linear transformations that are not commutative. • What operations is it true for? Multiplication evans@virginia.edu Engineering Crypto Applications 20
- 22. Diffie-Hellman(-Merkle) Key Agreement Whit Diffie evans@virginia.edu Martin Hellman Engineering Crypto Applications 21
- 23. Diffie-Hellman Key Agreement Alice Bob 1. Choose and publish: q (large prime number) (primitive root of q) 2. Generate random XA 4. Generate random XB. XA mod q. 3. Send YA= 5. Send YB= XB mod q. K = (YB) XA mod q evans@virginia.edu K = (YA)XB mod q Engineering Crypto Applications 22
- 24. Key Agreement Requirements Correctness: Both participants get the same key Security: An eavesdropper cannot find K from all intercepted values evans@virginia.edu Engineering Crypto Applications 23
- 25. Key Agreement Correctness Correctness: Both participants get the same key YA= XA mod q K = (YB) XA mod q evans@virginia.edu YB= XB mod q K = (YA)XB mod q Engineering Crypto Applications 24
- 26. Key Agreement Correctness Correctness: Both participants get the same key YA = XA mod q K = (YB) XA mod q YB= XB mod q K = (YA)XB mod q = ( XB mod q)XA mod q = ( XA mod q)XB mod q = ( XBXA mod q) mod q = ( XAXB mod q) mod q = XBXA mod q = XAXB mod q Multiplication commutes (just like the padlocks)! evans@virginia.edu Engineering Crypto Applications 25
- 27. Security Alice Bob 1. Choose and publish: q (large prime number) (primitive root of q) 2. Generate random XA 4. Generate random XB. XA mod q. 3. Send YA= 5. Send YB= XB mod q. K = (YB) XA mod q K = (YA)XB mod q An eavesdropper cannot find K from all intercepted values: q, , YA, YB evans@virginia.edu Engineering Crypto Applications 26
- 28. Primitive Roots is a primitive root of Bob for all q if 1 n < q, there is some m, 1. Choose and publish: 1 m < q such that q (large prime number) m = n mod q (primitive root of q) prime numbers have primitive All 2. Generate random XA roots. Alice 3. Send YA= XA mod q. 4. Generate random XB. 5. Send YB= XB mod q. Discrete logarithm problem: given , n, and q find the one 0 XA m < q such that K = mYB) mod q ( K = (YA)XB mod q = n mod q For good choices of q, this is believed to be hard. evans@virginia.edu Engineering Crypto Applications 27
- 29. Security of Diffie-Hellman DiscreteAlice logarithm problem: given , n, andBobfind q the one 0 m < q such 1. Choose and publish: that m = n mod q q (large prime number) For good choices of q, this is believed to be hard. (primitive root of q) 2. Generate random XA 4. Generate random XB. XA mod q. 3. Send YA= 5. Send Y = XB mod q. K = (YB) XA mod q B Eavesdropper cannot find K from intercepted values: q, , YA, YB If they could, could solve discrete log problem which is hard: given YA= XA mod q find XA evans@virginia.edu Engineering Crypto Applications 28
- 30. What about Mallory? Insecure Channel (e.g., the Internet) Ciphertext Plaintext Encrypt Decrypt Alice Plaintext Bob Mallory (active attacker) evans@virginia.edu Engineering Crypto Applications 29
- 31. Secure from Active Eavesdropper? Bob Alice Public: q, XB XA K = (YB) evans@virginia.edu XA mod K = (YA)XB mod q q Engineering Crypto Applications 30
- 32. Alice Bob Public: q, XB XA Mallory (active attacker) KAM = (YM) XA mod q evans@virginia.edu XM Engineering Crypto Applications KBM = (YM)XB mod q 31
- 33. Bob Alice Public: q, XB XA Mallory (active attacker) KAM = (YM) XA mod q XM KBM = (YM)XB mod q KAM = (YA) XM mod q KBM = (YB) XM mod q evans@virginia.edu Engineering Crypto Applications 32
- 34. Bob Alice Public: q, XB XA Mallory (active attacker) KAM = (YM) XA mod q XM KBM = (YM)XB mod q KAM = (YA) XM mod q KBM = (YB) XM mod q evans@virginia.edu Engineering Crypto Applications 33
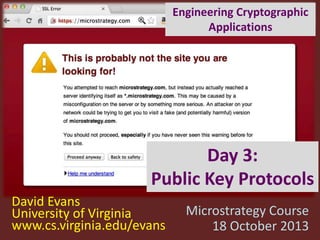
- 35. Does D-H Solve This? Insecure Channel petitions.gov How does TJ know he’s really talking to petitions.gov? How can he establish a secure channel to transmit password? evans@virginia.edu Engineering Crypto Applications 34
- 37. Asymmetry Required Messages: everyone should be able to send Alice a message that only Alice can read Signatures: Bob should be able to verify Alice signed a message, but not impersonate Alice evans@virginia.edu Engineering Crypto Applications 36
- 38. Asymmetric Cryptosystem Alice Plaintext E Bob Ciphertext D Plaintext Insecure Channel Correctness: D(E(m)) = m Security: given E(m) and E , cannot learn anything interesting about m or D evans@virginia.edu Engineering Crypto Applications 37
- 39. Asymmetric Cryptosystem (with Kerckhoffs’ Principle) Alice Plaintext Bob Ciphertext E D Plaintext Insecure Channel KUA KRA Correctness: DKU (EKR (m)) = m A A Security: given EKR (m), E, KUA, and D, cannot A learn anything interesting about m or KRA. evans@virginia.edu Engineering Crypto Applications 38
- 40. Providing Asymmetry Need a function f that is: Easy to compute: given x, easy to compute f (x) Hard to invert: given f (x), hard to compute x Has a trap-door: given f (x) and t, easy to compute x No function (publicly) known with these properties until 1977… evans@virginia.edu Engineering Crypto Applications 39
- 41. Len Adleman evans@virginia.edu Adi Shamir Engineering Crypto Applications Ron Rivest 40
- 43. RSA Cryptosystem Ee(M ) = Me mod n Dd(C ) = Cd mod n n = pq p, q are prime d is relatively prime to (p – 1)(q – 1) ed 1 mod (p – 1)(q – 1) evans@virginia.edu Engineering Crypto Applications 42
- 44. Correctness of RSA Ee(M ) = Me mod n Dd(C ) = Cd mod n evans@virginia.edu Engineering Crypto Applications 43
- 45. Correctness of RSA Ee(M ) = Me mod n Dd(C ) = Cd mod n Dd(Ee(M )) = (Me mod n)d mod n = Med mod n = M This step depends on choosing e and d to have this property: uses Fermat’s little theorem and Euler’s Totient theorem evans@virginia.edu Engineering Crypto Applications 44
- 46. Bonus: Works in Both Orders Ee(M ) = Me mod n Dd(C ) = Cd mod n Ee (Dd(M )) = (Md mod n)e mod n = Mde mod n =M evans@virginia.edu Engineering Crypto Applications 45
- 47. Providing Asymmetry Need a function f that is: Easy to compute: given x, easy to compute f (x) Hard to invert: given f (x), hard to compute x Has a trap-door: given f (x) and t, easy to compute x evans@virginia.edu Does RSA satisfy these? Engineering Crypto Applications 46
- 48. Easy (Enough) to Compute Easy to compute: given x, easy to compute f (x) Ee(M ) = evans@virginia.edu e mod M Engineering Crypto Applications n 47
- 49. Easy (Enough) to Compute Ee(M ) = Me mod n a m +n = a m × a n a2b = ab × ab Compute Me in about log2e multiplications Be careful not to have a timing side channel though! evans@virginia.edu Engineering Crypto Applications 48
- 50. Hard to Invert Given Ee(M ) and e and n, hard to compute M. If attacker can factor n = pq, easy to find d: d = e-1 mod (p – 1)(q – 1) All other attacks are equivalent to factoring n. No one seems to know a fast way to factor, except with a quantum computer (and no one seems to yet know how to build a large one). For reasonable security, n should be 2048 bits (comparable to 112-bit symmetric key) – believed sufficient until 2030. evans@virginia.edu Engineering Crypto Applications 49
- 51. Easy to Invert with Trapdoor e mod M Ee(M ) = n Dd(C ) = Cd mod n evans@virginia.edu Engineering Crypto Applications 50
- 52. Using RSA: Confidentiality Alice Sends confidential messages to Bob using his public key Plaintext E Bob Selects two large primes p, q Computes ed 1 mod (p – 1)(q – 1) Publishes n = pq and e, keeps d secret Ciphertext D Plaintext Insecure Channel KRB KUB Private Key: KRB = d Bob’s Public Key: KUB = (n, e) (private exponent) (modulus, public exponent) Over 1000x slower than AES! Only use when asymmetry is needed. evans@virginia.edu Engineering Crypto Applications 51
- 53. Using RSA: Signatures Alice Sends confidential messages to Bob using his public key Plaintext E Bob Selects two large primes p, q Computes ed 1 mod (p – 1)(q – 1) Publishes n = pq and e, keeps d secret Ciphertext D Plaintext Insecure Channel KRB KUB Private Key: KRB = d Bob’s Public Key: KUB = (n, e) (private exponent) (modulus, public exponent) Over 1000x slower than AES! Only use when asymmetry is needed. evans@virginia.edu Engineering Crypto Applications 52
- 54. Using RSA: Signatures Alice Verifies message is from Bob using his public key Verified Message E Bob Selects two large primes p, q Computes ed 1 mod (p – 1)(q – 1) Publishes n = pq and e, keeps d secret Signed Message D Message Insecure Channel KRB KUB Private Key: KRB = d Bob’s Public Key: KUB = (n, e) (private exponent) (modulus, public exponent) Over 1000x slower than AES! Only use when asymmetry is needed. evans@virginia.edu Engineering Crypto Applications 53
- 55. Elliptic Curve Asymmetric Cryptosystems Elliptic curve discrete logarithm problem: given points P and Q on an elliptic curve, it is hard to find an integer k such that Q = kP (unless you know trapdoor). evans@virginia.edu y2 = x3 – 7 (mod p) Engineering Crypto Applications 54
- 56. RSA 1977 ECC 1985 Discovery (previously discovered in 1969 by GHCQ and perhaps earlier by NSA) (adoption limited until ~2005) “Hard” Problem Factoring Discrete Log on Elliptic Curve Key Size (~112-bit) 2048 bits (768 bits broken) 224 bits (112 bits broken) Backdoor Risk None Curves selected by NSA Quantum Computing Risk Known fast factoring algorithms (Shor’s) Similar (variation of Shor’s algorithm solves Discrete Log) Implementation Challenges Avoiding weak keys, timing side channels Fast operations on elliptic curves, leaks on invalid inputs evans@virginia.edu Engineering Crypto Applications 55
- 57. RSA ECC 1985 Lattice Ciphers (adoption limited until ~2005) 1996 Factoring Discrete Log on Elliptic Curve Lattice Problems (e.g., closest vector) Key Size (~112-bit) 2048 bits (768 bits broken) 224 bits (112 bits broken) 1,000,000 bits Backdoor Risk None Curves selected by NSA Little Quantum Computing Risk Known fast factoring algorithms (Shor’s) Similar (variation of Shor’s algorithm solves Discrete Log) Only if P = NP Discovery 1977 “Hard” Problem Implementation Challenges evans@virginia.edu Avoiding weak Fast operations on keys, timing side elliptic curves, leaks channels Engineering Crypto Applications on invalid inputs Only simple arithmetic (but 10Ks of them) 56
- 58. Applications of Asymmetric Cryptosystems evans@virginia.edu Engineering Crypto Applications 57
- 59. Using Asymmetry: Signatures Alice Bob Verifies message is from Bob using his public key Verified Message E Generates KUB and KRB Publishes KUB Signed Message D Message Insecure Channel KRB KUB Over 1000x slower than AES! (with both RSA and ECC) What if we need to sign long (bigger than n ~ 2048 bits) messages? evans@virginia.edu Engineering Crypto Applications 58
- 60. Message Digests Alice Verified Verified Message Message Digest E Message D KRB KUB Message Digest H Signed Message = Bob Message H H is a cryptographic hash function: one-way: given H(x) cannot find preimage x strong collision-resistant: hard to find pair x and y where H(x) = H(y) evans@virginia.edu Engineering Crypto Applications 59
- 61. Authentication Insecure Channel petitions.gov How does TJ know he’s really talking to petitions.gov? How can he establish a secure channel to transmit password? evans@virginia.edu Engineering Crypto Applications 60
- 62. Simple Login Protocol Eve can’t decrypt without KRpetitions. petitions.gov EKUpetitions(“tj” + password) evans@virginia.edu Engineering Crypto Applications DKRpetitions(c) 61
- 63. Getting Public Keys • Public keys only useful if you know you have the right one! • Secure on-line directory? What is petitions.gov public key? keys.gov KUpetitions evans@virginia.edu Engineering Crypto Applications 62
- 64. Moving Directory Off-Line TrustMe.com petitions.gov, KUPetitions CP = KRTrustMe*“petitions.gov”, KUPetitions] TJ CP Verifies using KUTrustMe evans@virginia.edu Petitions Engineering Crypto Applications 63
- 65. Anyone use this? evans@virginia.edu Engineering Crypto Applications 64
- 68. SSL (Secure Sockets Layer) Simplified TLS Handshake Protocol Client Verify Certificate using KUCA Server Hello KRCA[Server Identity, KUS] Check identity matches URL Generate random K EKUS (K) Decrypt using KRS Secure channel using K evans@virginia.edu Engineering Crypto Applications 67
- 71. SSL (Secure Sockets Layer) Simplified TLS Handshake Protocol Client Verify Certificate using KUCA Check identity matches URL Generate random K Server Hello KRCA[Server Identity, KUS] How did client get KUCA? EKUS (K) Decrypt using KRS Secure channel using K evans@virginia.edu Engineering Crypto Applications 70
- 73. How does VarySign decide if it should give certificate to requester? Certificates VarySign.com petitions.gov, KUPetitions CP = KRVarySign*“petitions.gov”, KUPetitions] TJ CP Verifies using KUVarySign evans@virginia.edu Petitions Engineering Crypto Applications 72
- 74. $1500 for 1 year evans@virginia.edu Engineering Crypto Applications $399 73
- 76. Limiting Damage VarySign.com petitions.gov, KUPetitions CP = KRVarySign *“petitions.gov”, cert ID, Expiration, KUPetitions] TJ CP Verifies using KUVarySign evans@virginia.edu Petitions Engineering Crypto Applications 75
- 77. Certificate Revocation Certificate Revocation List (CRL) <cert ID, date> … VarySign.com petitions.gov, KUPetitions CP = KRVarySign*“petitions.gov”, cert ID, Expiration, KUPetitions] Client CP Petitions Verifies using KUVarySign evans@virginia.edu Engineering Crypto Applications 76
- 78. CRL Checking Mozilla Firefox Google Chrome On-line checking is expensive and may fail Attacker-in-the-middle can make it fail evans@virginia.edu Engineering Crypto Applications 77
- 79. SSL (Secure Sockets Layer) Simplified TLS Handshake Protocol Client Server Hello some extra steps: Verify Actual TLS hasKRCA[Server Identity, KUS] Certificate using KUCA - Negotiate versions CheckAgree - identity matches URL on which ciphers to use (many options, but beware!) Generate Decrypt -randomauthenticate client also Can K KU (K) E [K] KUS S using KRS Secure channel using K evans@virginia.edu Engineering Crypto Applications 78
- 80. Summary • Many useful applications require asymmetry – Confidentiality without shared key, signatures – Others we will cover next week • Asymmetric cryptosystems can be built using hard problems in number theory with trapdoors: RSA (factoring), ECC (discrete log) • Asymmetric ciphers are very expensive: need to combine with hashes and symmetric crypto evans@virginia.edu Engineering Crypto Applications 79
- 81. SSL Test evans@virginia.edu Engineering Crypto Applications 80
- 83. Plan for Final Meeting: Applications of Asym Crypto Secure Computation Future of Cryptosystems open to requests! evans@virginia.edu MightBeEvil.com/crypto evans@virginia.edu Engineering Crypto Applications 82
