Growth Hack Checklist: Test, Measure, Optimize
•Als DOCX, PDF herunterladen•
0 gefällt mir•200 views
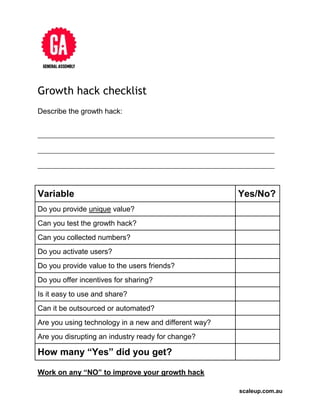
This document provides a checklist for evaluating potential growth hacks. It asks the user to describe the growth hack and then asks a series of yes/no questions to determine if the hack provides unique value, can be tested and tracked with numbers, activates users and their friends, offers incentives for sharing, is easy to use and share, can be outsourced or automated, uses technology in a new way, disrupts an industry, and encourages the user to improve any hacks that received negative answers.
Melden
Teilen
Melden
Teilen
Empfohlen
Weitere ähnliche Inhalte
Mehr von Bjarne Viken
Mehr von Bjarne Viken (20)
TURNAPROFITINTRODUCTIONTOCONVERSIONOPTIMIZATIONWORKBOOK

TURNAPROFITINTRODUCTIONTOCONVERSIONOPTIMIZATIONWORKBOOK
Google Analytics- Start Turning Data Into Actionable Insights

Google Analytics- Start Turning Data Into Actionable Insights
What to look for in a freelancers profile on odesk

What to look for in a freelancers profile on odesk
How to use incentives actively to increase revenue

How to use incentives actively to increase revenue
How to set up an almost completely automated social media strategy 

How to set up an almost completely automated social media strategy
How to create long lasting relationships with freelancers

How to create long lasting relationships with freelancers
How to communicate with graphic designers to make a great site

How to communicate with graphic designers to make a great site
How to communicate with graphic designers to make a great site in as little t...

How to communicate with graphic designers to make a great site in as little t...
How to communicate with graphic designer to make a great site

How to communicate with graphic designer to make a great site
Growth Hack Checklist: Test, Measure, Optimize
- 1. scaleup.com.au Growth hack checklist Describe the growth hack: __________________________________________________________________________ __________________________________________________________________________ __________________________________________________________________________ Variable Yes/No? Do you provide unique value? Can you test the growth hack? Can you collected numbers? Do you activate users? Do you provide value to the users friends? Do you offer incentives for sharing? Is it easy to use and share? Can it be outsourced or automated? Are you using technology in a new and different way? Are you disrupting an industry ready for change? How many “Yes” did you get? Work on any “NO” to improve your growth hack
